Session Video
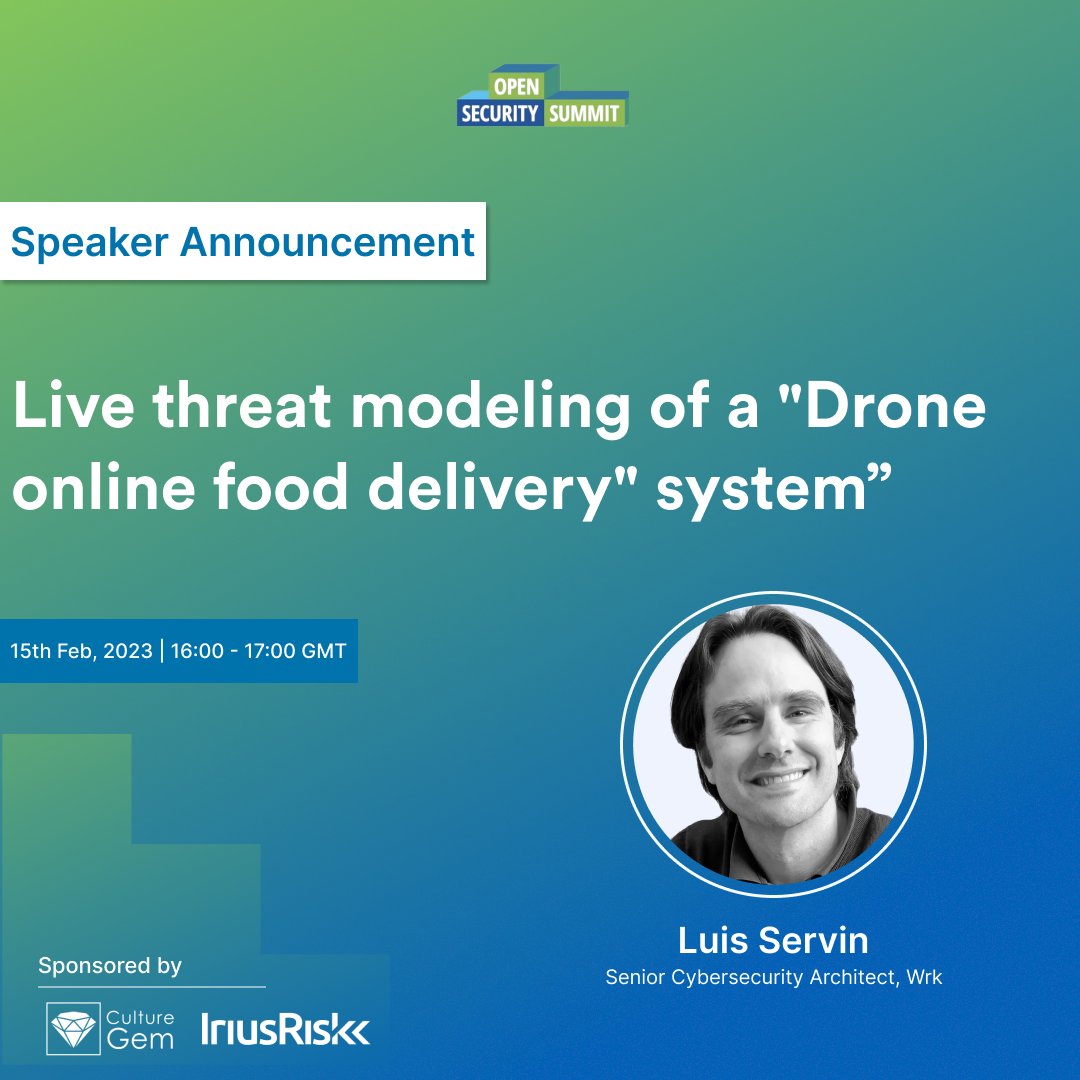
About this session
When learning threat modeling, there is a need for examples that are well thought out. Since DefCon 27 there is a threat modeling competition called “DEF CON’s Next Top Threat Model” (https://threatmodel.us). The system described in this competition is a perfect example to find possible threats and evaluate them. The system described allows users to order food using a kiosk that also charges the customer’s credit card and prints the order in the kitchen printer. In this session we’ll analyze the system: draw diagrams using the C4 modeling technique (https://c4model.com/) to understand what are we building. Then we’ll start looking for anything that could go wrong and what we could do about it. It will be an interactive session where audience participation is actively encouraged.

 Luis Servin
Luis Servin